-
Two Layers of Added Security
2-Factor Authentication
Passwords provide you with added security to keep prying eyes away from your information and data. Most people have one layer (their password) to protect their account. 2-Factor Authentication adds a second level of security to your account.
-
Password Managers
Everything you need to know
A password manager tool is software that helps users to encrypt, store, and manage passwords. The tool also helps users to create secure passwords and automatically log into websites.
-
Encrypt Zip Files
for Windows and Mac
Learn how to encrypt zip files or folders for Windows, Mac OS, and Linux machines. Protect your confidential and personal data!
-
What Apps Have Access to Your Facebook and Twitter?
Learn how to audit Facebook and Twitter, so you can control what apps have access to your personal data and reduce your risk of unauthorized use of these apps, cut down on the chances of spammers taking over your account, and even remind yourself of tools and services you may have forgotten about.
-
Important Security Measure for iPhones
It's easier than you think for someone to get into your Apple products -- even if a thief doesn't have the actual iPhone in his or her hands. How to make yourself much safer?
-
Why Use Anti-Virus Software?
Learn why anti-virus software is not just a good idea, but can be a work saver!
-
About the Information Security Office
The Information Security Office leads efforts to implement industry and higher education best practices in information security.
-
The Internet of Things
As the cost of connecting to the Internet has gone down, more and more everyday devices are being made to connect online. These devices, which make up the Internet of Things, introduce new security challenges.
-
Spearphishing
A different kind of fishing
Emails are a great way to communicate with someone. However, be wary of messages, especially from people you don't know, that asks you for personal information or tells you to click on a link. You never know when someone is fishing for your information. Learn more here.
-
Change your Twitter Password
Twitter has discovered a bug that internally stored user passwords in plaintext and is urging users to change their passwords.
-
Summer Scams
Scammers don't take a break during the summer months; in fact, they may be ramping up their attacks to exploit your extra time online, vacation plans, or desire to improve yourself and your home. Make sure you're aware of these common attacks so you can keep your money and information safe from fraudsters.
-
Google Drive Sharing Instructions
It's important to understand exactly how you are using Google Drive so you don't accidentally share sensitive personal or university information. Check out this guide, and you might learn something to make your work more efficient, too!
-
Back Up Your Personal Devices
No matter how careful you are, there is always a chance your device or computer can be lost, stolen, infected with malware, or simply stop working. Keeping regular backups of the data on your personal devices will give you peace of mind and ensure you don’t lose family photos or important records and assignments.
-
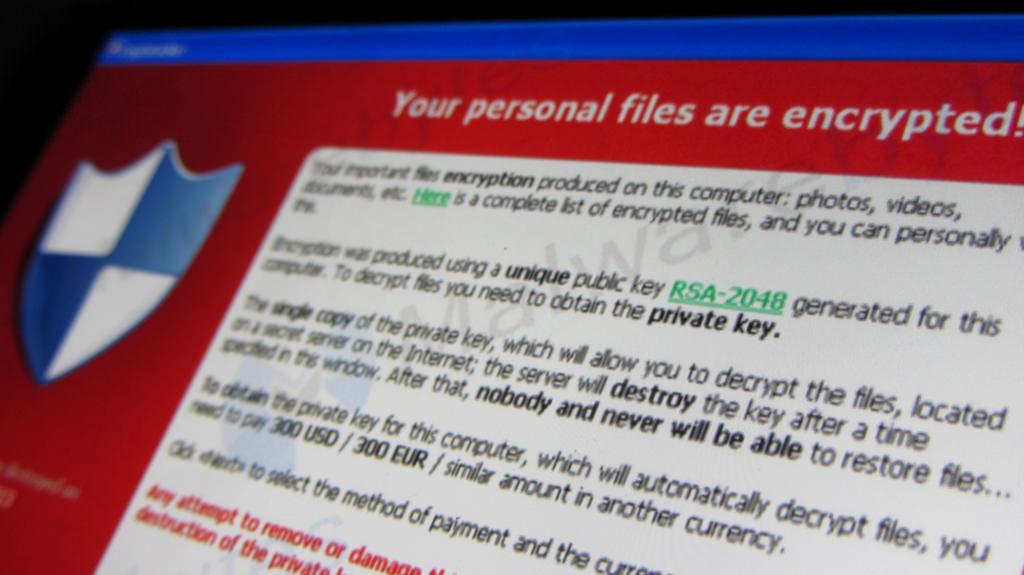
Ransomware
What is ransomware? What should you do if it takes control of your system?
-
Back-to-School CyberSecurity Tips
Protect your wallet and your account by watching out for these common cyber-scams! (September 23, 2019)
-
Social Engineering
Don't be the one to hand over information to an attacker!
Social engineering is one of the most effective and least recognized hacking methods, and attackers often don't even need to write a line of code. Find out what it looks like and how to avoid it.
-
Disposing of Your Mobile Device
Upgrading your mobile phone soon? Learn how to securely wipe your information so it doesn't fall into the wrong hands! (March 6, 2019)
-
Starting a Career in Information Security
At current projections, it is estimated there will be a shortfall of 1.8 million information security workers by 2022. If cybersecurity is of interest, this is definitely a growing field. It is vitally important that as a current student, you will graduate ready to enter the workforce to fill one of the vast numbers of positions available.
-
2022 Cybersecurity Awareness Month: Phishing
How To Keep Phishing At Bay
Some tips on how to protect yourself against email/phone/text phishing
-
Making Passwords Simple
Here are three simple steps to simplify your passwords, lock down your accounts, and protect your future. (April 3, 2019)
-
Women in Information Security
Diversity in the technology industry in necessary to stay a step ahead of cybercrime.
Women make up only 10% of the Information Security workforce. Why are women so underrepresented? What can be done to change that?
-
Protect your Personal Information from Phone and Laptop Thieves
No matter what, you will never be able to guarantee your laptop, phone, and tablet cannot be stolen or lost. Find out how to protect your sensitive information even in the event you lose your device.
-
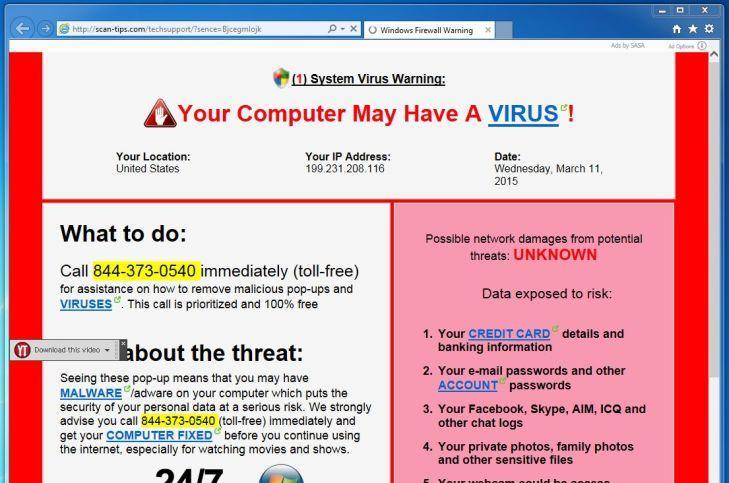
Tech Support Scams
Tech support scams are a particularly sneaky approach criminals use to make money off of people’s trust. It is important that all Santa Clara University students, faculty, and staff know how to identify these scams to protect individual and university resources.